-
 Data Processing Agreement checklistEveryone tells their teams to do their due diligence, but do they know what that actually looks like? This job aid gives your IT and procurement teams the ultimate vendor contract checklist, covering everything from contract basics to data-processing...8✨Tokens
Data Processing Agreement checklistEveryone tells their teams to do their due diligence, but do they know what that actually looks like? This job aid gives your IT and procurement teams the ultimate vendor contract checklist, covering everything from contract basics to data-processing...8✨Tokens -
 Information been stolen? Report it! - horizontalUse this straightforward piece to remind your employees that they shouldn't hide when something goes missing, but should raise their hand immediately.2✨Tokens
Information been stolen? Report it! - horizontalUse this straightforward piece to remind your employees that they shouldn't hide when something goes missing, but should raise their hand immediately.2✨Tokens -
 Away from your computer? - horizontalMake sure your team always remembers: an open computer, left alone, is a privacy breach waiting to happen.2✨Tokens
Away from your computer? - horizontalMake sure your team always remembers: an open computer, left alone, is a privacy breach waiting to happen.2✨Tokens -
 Information been stolen? Report it!Use this straightforward piece to remind your employees that they shouldn't hide when something goes missing, but should raise their hand immediately.2✨Tokens
Information been stolen? Report it!Use this straightforward piece to remind your employees that they shouldn't hide when something goes missing, but should raise their hand immediately.2✨Tokens -
 Mix it up: password guidanceWant a smoothie? Well, here's a smooth (ay!) way to remember to set up complex passwords.2✨Tokens
Mix it up: password guidanceWant a smoothie? Well, here's a smooth (ay!) way to remember to set up complex passwords.2✨Tokens -
 This is not where your password belongsMake sure your team knows their passwords are supposed to be secret—-not out where someone can find them, especially on their desks.2✨Tokens
This is not where your password belongsMake sure your team knows their passwords are supposed to be secret—-not out where someone can find them, especially on their desks.2✨Tokens -
 Protect your password!Give your folks these simple rules to lock down their passwords—and protect your info.2✨Tokens
Protect your password!Give your folks these simple rules to lock down their passwords—and protect your info.2✨Tokens -
 Away from your computer?Make sure your team always remembers: an open computer, left alone, is a privacy breach waiting to happen.2✨Tokens
Away from your computer?Make sure your team always remembers: an open computer, left alone, is a privacy breach waiting to happen.2✨Tokens -
 Privacy screens—use them!Privacy screens are vital to prevent data breaches, even if they're a little annoying. (On the upside, you can watch your favorite horror movie on the plane without terrifying the toddler next to you.)2✨Tokens
Privacy screens—use them!Privacy screens are vital to prevent data breaches, even if they're a little annoying. (On the upside, you can watch your favorite horror movie on the plane without terrifying the toddler next to you.)2✨Tokens -
 We don't conduct business on personal emailsMake sure your team is alert for when people try to take business on to their personal emails—it may be a scam.2✨Tokens
We don't conduct business on personal emailsMake sure your team is alert for when people try to take business on to their personal emails—it may be a scam.2✨Tokens -
 Get asked to click on a link?Spelling is hard! But also potentially a sign of fraud. This simple reminder puts sketchy web addresses on your folks' radar.2✨Tokens
Get asked to click on a link?Spelling is hard! But also potentially a sign of fraud. This simple reminder puts sketchy web addresses on your folks' radar.2✨Tokens -
NEW



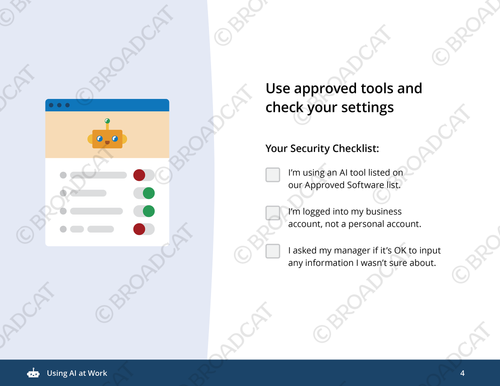 Using AI at WorkYour employees use AI to brainstorm, draft, and code at warp speed. But there’s a massive gap between "hit generate" and "hit send" that can lead to some pretty messy hallucinations and data leaks. This mini-module doubles down on why being the...8✨Tokens
Using AI at WorkYour employees use AI to brainstorm, draft, and code at warp speed. But there’s a massive gap between "hit generate" and "hit send" that can lead to some pretty messy hallucinations and data leaks. This mini-module doubles down on why being the...8✨Tokens -
 Is that QR code safe?Everywhere you look there’s a QR code begging to be scanned, but it's not always clear what lurks behind those mysterious black and white patterns. Help your teams stay vigilant with this ingenious awareness material, which calls out red flags in...4✨Tokens
Is that QR code safe?Everywhere you look there’s a QR code begging to be scanned, but it's not always clear what lurks behind those mysterious black and white patterns. Help your teams stay vigilant with this ingenious awareness material, which calls out red flags in...4✨Tokens -
 Insider threat red flagsEducate your employees on what insider threats are, where they come from, and some common red flag behaviors. This infographic kicks things off with a not-so-obvious concept: that insider threats don’t necessarily come from inside the...8✨Tokens
Insider threat red flagsEducate your employees on what insider threats are, where they come from, and some common red flag behaviors. This infographic kicks things off with a not-so-obvious concept: that insider threats don’t necessarily come from inside the...8✨Tokens -
 Video: Want to collect customer data?Your employees need to collect personal data—but what they need to think through beforehand isn’t always clear. This video (less than 2 minutes) tells your employees the 5 W’s and sometimes H of collecting personal data, why you...10✨Tokens
Video: Want to collect customer data?Your employees need to collect personal data—but what they need to think through beforehand isn’t always clear. This video (less than 2 minutes) tells your employees the 5 W’s and sometimes H of collecting personal data, why you...10✨Tokens -
 Awareness Campaign: Around the workplaceRemind your employees who’s responsible for compliance at your org (hint: EVERYONE!) with these clever signs around the office. Sometimes we forget to do some of the simplest things as we go about our days, like observing who’s around us...8✨Tokens
Awareness Campaign: Around the workplaceRemind your employees who’s responsible for compliance at your org (hint: EVERYONE!) with these clever signs around the office. Sometimes we forget to do some of the simplest things as we go about our days, like observing who’s around us...8✨Tokens -
 How to protect our data from impostersKids dressing up as police officers = super cute. Adults impersonating them to get your company’s data = just plain creepy. But do your employees know what to do if they get a strange data request? Use this infographic to highlight who scammers are...8✨Tokens
How to protect our data from impostersKids dressing up as police officers = super cute. Adults impersonating them to get your company’s data = just plain creepy. But do your employees know what to do if they get a strange data request? Use this infographic to highlight who scammers are...8✨Tokens -
 Privacy screens—use them! - horizontalPrivacy screens are vital to prevent data breaches, even if they're a little annoying. (On the upside, you can watch your favorite horror movie on the plane without terrifying the toddler next to you.)2✨Tokens
Privacy screens—use them! - horizontalPrivacy screens are vital to prevent data breaches, even if they're a little annoying. (On the upside, you can watch your favorite horror movie on the plane without terrifying the toddler next to you.)2✨Tokens -
 Recycle paper, not passwords - horizontalRecycling may be great for the environment, but it's terrible for cybersecurity! Remind your team of the need to protect your data with unique passwords.2✨Tokens
Recycle paper, not passwords - horizontalRecycling may be great for the environment, but it's terrible for cybersecurity! Remind your team of the need to protect your data with unique passwords.2✨Tokens -
 Found USBs = found gumEnsure your employees are grossed out at the security risk of using an unknown USB.2✨Tokens
Found USBs = found gumEnsure your employees are grossed out at the security risk of using an unknown USB.2✨Tokens -
 Protect your passwordA helpful reminder to be smart with passwords to protect company info.2✨Tokens
Protect your passwordA helpful reminder to be smart with passwords to protect company info.2✨Tokens -
 Click smart!Keep your team thinking about safe web use.2✨Tokens
Click smart!Keep your team thinking about safe web use.2✨Tokens -
 Recycle paper, not passwordsRecycling may be great for the environment, but it's terrible for cybersecurity! Remind your team of the need to protect your data with unique passwords.2✨Tokens
Recycle paper, not passwordsRecycling may be great for the environment, but it's terrible for cybersecurity! Remind your team of the need to protect your data with unique passwords.2✨Tokens -
 Share pencils, not passwordsSharing is caring! Except when it comes to passwords.2✨Tokens
Share pencils, not passwordsSharing is caring! Except when it comes to passwords.2✨Tokens

