-
 Destroy It SecurelyThis simple graphic instructs your team that shredding—not the trash can—is how you get rid of docs securely.2✨Tokens
Destroy It SecurelyThis simple graphic instructs your team that shredding—not the trash can—is how you get rid of docs securely.2✨Tokens -
 Awareness campaign: AI chatbotsLet’s be real: Your employees are already using generative AI and chatbots to boost their work. Before they slip up and accidentally share sensitive information or breach IP protections, display these awareness materials where they’ll...5✨Tokens
Awareness campaign: AI chatbotsLet’s be real: Your employees are already using generative AI and chatbots to boost their work. Before they slip up and accidentally share sensitive information or breach IP protections, display these awareness materials where they’ll...5✨Tokens -



 Module: Annual Refresher CourseStill stuck doing annual check-the-box training? Gross, and sorry. But hey, at least this 31-slide kit will make it 10 minutes long and actually relevant to every employee. So, you've got that going for you, which is nice. The ideal annual refresher...25✨Tokens
Module: Annual Refresher CourseStill stuck doing annual check-the-box training? Gross, and sorry. But hey, at least this 31-slide kit will make it 10 minutes long and actually relevant to every employee. So, you've got that going for you, which is nice. The ideal annual refresher...25✨Tokens -
 Before a merger or acquisition...Mergers and acquisitions can be both exciting and terrifying, like base jumping, that long drop on a rollercoaster, or attending a social event for us introverts. While we don’t have a remedy for that weird stomach feeling, we do have a solution to...8✨Tokens
Before a merger or acquisition...Mergers and acquisitions can be both exciting and terrifying, like base jumping, that long drop on a rollercoaster, or attending a social event for us introverts. While we don’t have a remedy for that weird stomach feeling, we do have a solution to...8✨Tokens -
 TMI? Let us know!Make it clear that self-reporting isn’t just OK, it’s expected. When humans handle data, there’s room for human error, so if someone on your team uncovers data they don’t need—or shouldn’t have—empower them to...2✨Tokens
TMI? Let us know!Make it clear that self-reporting isn’t just OK, it’s expected. When humans handle data, there’s room for human error, so if someone on your team uncovers data they don’t need—or shouldn’t have—empower them to...2✨Tokens -
 Make sure you have permissionGet straight to the point with this graphic: If you don’t have permission—or don’t know if you have permission—contact the Privacy Team.2✨Tokens
Make sure you have permissionGet straight to the point with this graphic: If you don’t have permission—or don’t know if you have permission—contact the Privacy Team.2✨Tokens -
 Data Processing Agreement checklistEveryone tells their teams to do their due diligence, but do they know what that actually looks like? This job aid gives your IT and procurement teams the ultimate vendor contract checklist, covering everything from contract basics to data-processing...8✨Tokens
Data Processing Agreement checklistEveryone tells their teams to do their due diligence, but do they know what that actually looks like? This job aid gives your IT and procurement teams the ultimate vendor contract checklist, covering everything from contract basics to data-processing...8✨Tokens -
 Interacting with clients and service providersWhile treating customers and vendors with respect is the right thing to do, it’s also great for business. Avoid helpline complaints and negative reviews (including on job search sites) by explaining exactly what civility and respect look like when...8✨Tokens
Interacting with clients and service providersWhile treating customers and vendors with respect is the right thing to do, it’s also great for business. Avoid helpline complaints and negative reviews (including on job search sites) by explaining exactly what civility and respect look like when...8✨Tokens -
 Information been stolen? Report it! - horizontalUse this straightforward piece to remind your employees that they shouldn't hide when something goes missing, but should raise their hand immediately.2✨Tokens
Information been stolen? Report it! - horizontalUse this straightforward piece to remind your employees that they shouldn't hide when something goes missing, but should raise their hand immediately.2✨Tokens -
 Shred it! (blue version) - horizontalIt's not hard, but it can be boring. Use this super-graphic piece to remind your team to shred confidential information—each and every time.2✨Tokens
Shred it! (blue version) - horizontalIt's not hard, but it can be boring. Use this super-graphic piece to remind your team to shred confidential information—each and every time.2✨Tokens -
 Mark it, protect itMaking sure confidential documents stay private requires some basics. This graphic guide helps your employees keep your info from accidentally getting disclosed by promoting uniformity in marking documents confidential—making it easier to recognize...6✨Tokens
Mark it, protect itMaking sure confidential documents stay private requires some basics. This graphic guide helps your employees keep your info from accidentally getting disclosed by promoting uniformity in marking documents confidential—making it easier to recognize...6✨Tokens -
 Keep confidential computer stuff on your computerProtect your company's data with this helpful graphic showing your team not to take photos of what's on their work computers.2✨Tokens
Keep confidential computer stuff on your computerProtect your company's data with this helpful graphic showing your team not to take photos of what's on their work computers.2✨Tokens -
 Social Media for Sensitive ProjectsDon’t let your employees give away secret information for free. This handy decision tree shows employees the potential pitfalls of social media use while working on highly confidential matters. Postings pics, tagging coworkers/vendors, checking...8✨Tokens
Social Media for Sensitive ProjectsDon’t let your employees give away secret information for free. This handy decision tree shows employees the potential pitfalls of social media use while working on highly confidential matters. Postings pics, tagging coworkers/vendors, checking...8✨Tokens -
 Information been stolen? Report it!Use this straightforward piece to remind your employees that they shouldn't hide when something goes missing, but should raise their hand immediately.2✨Tokens
Information been stolen? Report it!Use this straightforward piece to remind your employees that they shouldn't hide when something goes missing, but should raise their hand immediately.2✨Tokens -
 Protect your password!Give your folks these simple rules to lock down their passwords—and protect your info.2✨Tokens
Protect your password!Give your folks these simple rules to lock down their passwords—and protect your info.2✨Tokens -
 Away from your computer?Make sure your team always remembers: an open computer, left alone, is a privacy breach waiting to happen.2✨Tokens
Away from your computer?Make sure your team always remembers: an open computer, left alone, is a privacy breach waiting to happen.2✨Tokens -

 Shred it! (blue version)It's not hard, but it can be boring. Use this super-graphic piece to remind your team to shred confidential information—each and every time.2✨Tokens
Shred it! (blue version)It's not hard, but it can be boring. Use this super-graphic piece to remind your team to shred confidential information—each and every time.2✨Tokens -
 Shred it! (red shredder version)This attention-getter connects protecting your confidential info with the simple command to shred.2✨Tokens
Shred it! (red shredder version)This attention-getter connects protecting your confidential info with the simple command to shred.2✨Tokens -
 Privacy screens—use them!Privacy screens are vital to prevent data breaches, even if they're a little annoying. (On the upside, you can watch your favorite horror movie on the plane without terrifying the toddler next to you.)2✨Tokens
Privacy screens—use them!Privacy screens are vital to prevent data breaches, even if they're a little annoying. (On the upside, you can watch your favorite horror movie on the plane without terrifying the toddler next to you.)2✨Tokens -
NEW
 Parting ways: Your guide to a professional exitWhen someone’s leaving the org, the transition period can get a little messy. This checklist gives them the clarity they need to exit with their reputation—and yours—totally intact. We’ve covered the essential digital...6✨Tokens
Parting ways: Your guide to a professional exitWhen someone’s leaving the org, the transition period can get a little messy. This checklist gives them the clarity they need to exit with their reputation—and yours—totally intact. We’ve covered the essential digital...6✨Tokens -
NEW



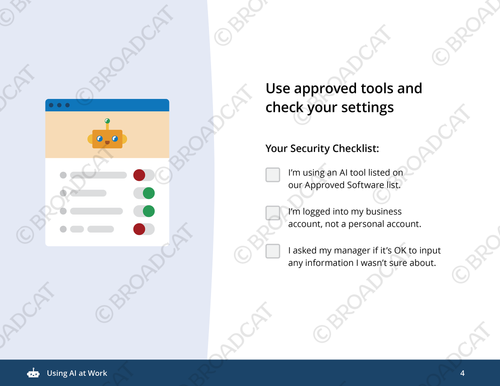 Using AI at WorkYour employees use AI to brainstorm, draft, and code at warp speed. But there’s a massive gap between "hit generate" and "hit send" that can lead to some pretty messy hallucinations and data leaks. This mini-module doubles down on why being the...8✨Tokens
Using AI at WorkYour employees use AI to brainstorm, draft, and code at warp speed. But there’s a massive gap between "hit generate" and "hit send" that can lead to some pretty messy hallucinations and data leaks. This mini-module doubles down on why being the...8✨Tokens -
NEW
 Video: Is this app OK for work?Your employees love their chat and collab apps. And can you blame them? A quick DM is instant gratification—unlike the slow death of waiting on an email reply. But those "off-channel" interactions can create a recordkeeping nightmare—and...8✨Tokens
Video: Is this app OK for work?Your employees love their chat and collab apps. And can you blame them? A quick DM is instant gratification—unlike the slow death of waiting on an email reply. But those "off-channel" interactions can create a recordkeeping nightmare—and...8✨Tokens -
 Video: Protect yourself and the company from insider tradingInsider trading…the term might conjure up an intense movie scene with people in fancy suits yelling on the phone. All very dramatic. But in the real world, the line isn’t always so clear. That's where this video comes in. It skips the legal...10✨Tokens
Video: Protect yourself and the company from insider tradingInsider trading…the term might conjure up an intense movie scene with people in fancy suits yelling on the phone. All very dramatic. But in the real world, the line isn’t always so clear. That's where this video comes in. It skips the legal...10✨Tokens -
 Insider threat red flagsEducate your employees on what insider threats are, where they come from, and some common red flag behaviors. This infographic kicks things off with a not-so-obvious concept: that insider threats don’t necessarily come from inside the...8✨Tokens
Insider threat red flagsEducate your employees on what insider threats are, where they come from, and some common red flag behaviors. This infographic kicks things off with a not-so-obvious concept: that insider threats don’t necessarily come from inside the...8✨Tokens

